Top 10 Things to Do After a Data Breach
Digital safety is no longer something only IT teams need to understand. Every login, message, download, phone setting, browser choice, and shared Wi-Fi network can affect your privacy, money, reputation, and peace of mind. This SenseCentral guide on Top 10 Things to Do After a Data Breach is written for everyday users, families, remote workers, creators, and small business owners who want practical protection without becoming security experts.
The good news is that strong cybersecurity does not always require expensive tools. Most real-world protection comes from consistent habits: using unique passwords, enabling two-factor authentication, updating devices, checking links before clicking, backing up files, and teaching family members how scams work. Small actions repeated every day can reduce the biggest risks.
This post breaks the topic into ten simple sections, includes a quick comparison table, adds useful resources, and finishes with FAQs and key takeaways. You can use it as a personal checklist, a family safety guide, or a training article for your team. The advice is general educational information, so always follow the latest guidance from your bank, device provider, employer, and local cybercrime reporting authority when dealing with serious incidents.
Quick Overview: Quick Cyber Safety Comparison
| Area | Safer Habit | Why It Adds Value |
|---|---|---|
| Risk 1 | Confirm whether your data was actually involved | Lower chance of account takeover, scams, data loss, or privacy exposure. |
| Risk 2 | Change the password for the affected account | Lower chance of account takeover, scams, data loss, or privacy exposure. |
| Risk 3 | Change reused passwords on every other account | Lower chance of account takeover, scams, data loss, or privacy exposure. |
| Risk 4 | Turn on two-factor authentication immediately | Lower chance of account takeover, scams, data loss, or privacy exposure. |
| Risk 5 | Watch bank, card, and payment activity closely | Lower chance of account takeover, scams, data loss, or privacy exposure. |
| Risk 6 | Beware of follow-up phishing messages after the breach | Lower chance of account takeover, scams, data loss, or privacy exposure. |
Cybersecurity can feel complicated, but the best starting point is simple: protect the accounts and devices that would cause the most damage if someone else controlled them. The following ten habits make the topic practical and easier to apply in everyday life.
1. Confirm whether your data was actually involved
Confirm whether your data was actually involved is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
2. Change the password for the affected account
Change the password for the affected account is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
3. Change reused passwords on every other account
Change reused passwords on every other account is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
4. Turn on two-factor authentication immediately
Turn on two-factor authentication immediately is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
5. Watch bank, card, and payment activity closely
Watch bank, card, and payment activity closely is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
6. Beware of follow-up phishing messages after the breach
Beware of follow-up phishing messages after the breach is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
7. Review account recovery information
Review account recovery information is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
8. Download important records if the service may be unstable
Download important records if the service may be unstable is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
9. Freeze or monitor credit when financial identity data is exposed
Freeze or monitor credit when financial identity data is exposed is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
10. Document what happened and keep breach notices safely
Document what happened and keep breach notices safely is important because attackers usually look for the easiest opening, not the most complicated one. For everyday users, the safest approach is to slow down, verify what you see, and avoid treating convenience as a replacement for protection. When applying this habit, start with your most valuable accounts: email, banking, cloud storage, social media, shopping, and work tools. Then extend the same habit to family devices, old accounts, and apps you use only occasionally. A practical rule is to ask, “Would this action expose my money, identity, personal photos, business data, or contacts if something went wrong?” If the answer is yes, add an extra layer of caution. In the context of Top 10 Things to Do After a Data Breach, this single step can prevent many common mistakes before they become expensive problems.
Practical action step
Open the relevant app, account, or device setting today and make one small improvement connected to this point. Do not try to fix everything in one sitting. A steady weekly checklist is easier to maintain than a one-time security cleanup that is never repeated.
Useful Resources for Readers and Creators
[Explore Our Powerful Digital Products] Browse these high-value bundles for website creators, developers, designers, startups, content creators, and digital product sellers.
Explore Our Powerful Digital Products
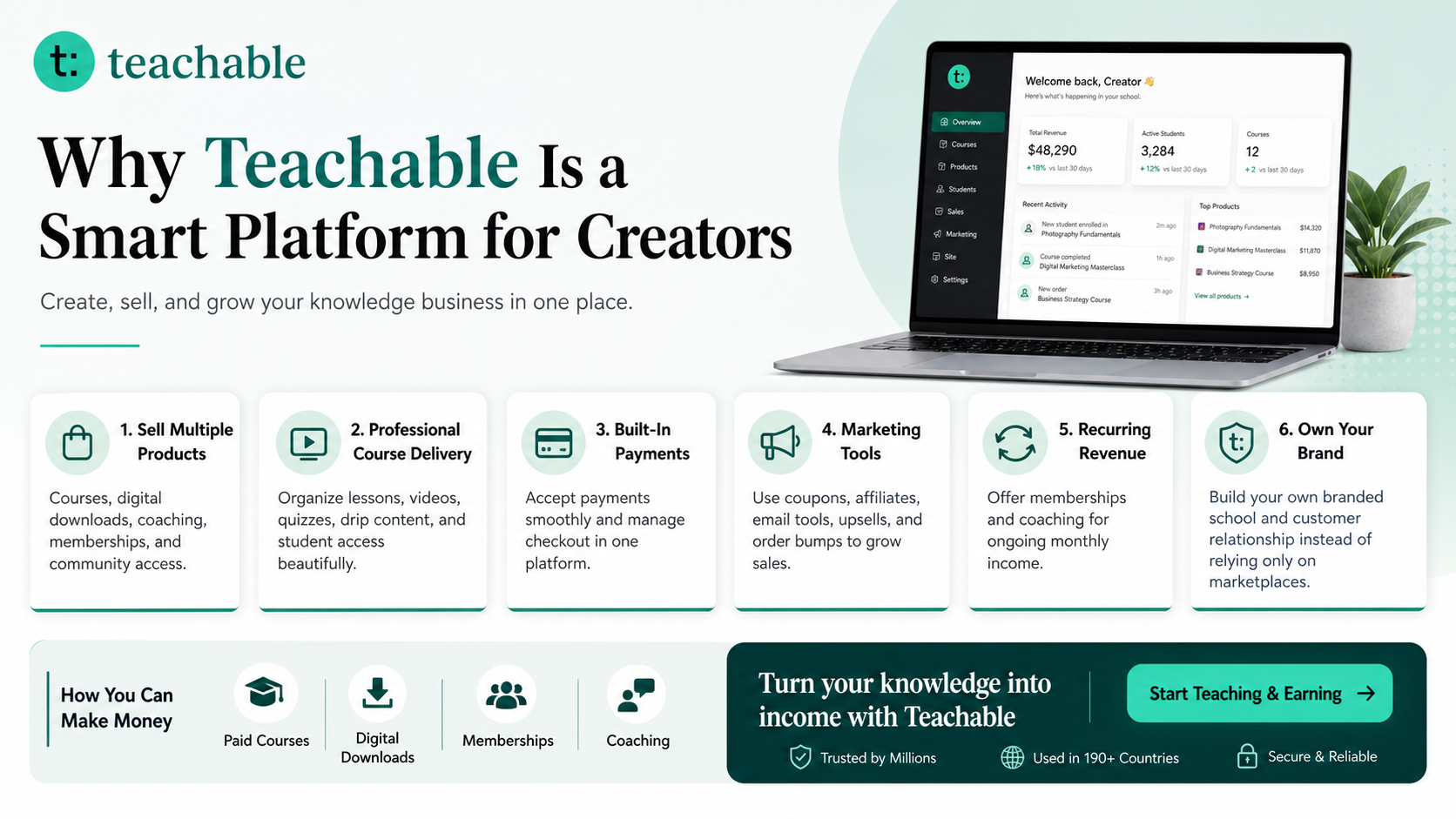
If you teach online, sell digital downloads, create guides, run a coaching business, or want to turn your knowledge into a product, Teachable can be a useful platform to explore.
Teachable is an online platform that lets creators build, market, and sell courses, digital downloads, coaching, and memberships. It helps educators and entrepreneurs turn their knowledge into a branded digital business without needing complex coding.
How to Make Money with Teachable: A Complete Creator’s Guide
More from SenseCentral: Visit SenseCentral • Search related guides on SenseCentral • Explore digital product ideas
Key Takeaways
- Security improves when small habits become automatic.
- Email, banking, phone, and cloud accounts deserve the strongest protection.
- Scams often use urgency, fear, trust, or curiosity to make people act quickly.
- Backups, updates, unique passwords, and two-factor authentication solve many common problems.
- Families and small teams should discuss digital safety before an incident happens.
FAQs
Is this advice enough to keep me completely safe online?
No guide can guarantee complete safety, but strong daily habits reduce common risks. Combine these tips with updated devices, trusted security tools, bank alerts, and caution around unexpected messages.
What is the first cybersecurity habit I should start with?
Start with your email account because it controls password resets for many other services. Use a unique password, enable two-factor authentication, and review recovery options.
Should families discuss online scams with children and older relatives?
Yes. Scammers often target people through emotion, urgency, curiosity, and trust. Simple conversations can help family members pause before clicking, paying, sharing OTPs, or responding to unknown contacts.
Are password managers safe for everyday users?
A reputable password manager can help create and store unique passwords. Protect it with a strong master password and two-factor authentication, and follow the provider’s safety guidance.
What should I do if I think I clicked a suspicious link?
Disconnect if needed, avoid entering more information, change relevant passwords from a safe device, enable two-factor authentication, scan for malware, monitor accounts, and report the incident to the right platform or authority.
Further Reading and References
Use these helpful external references to continue learning from trusted organizations and documentation sources:
- CISA Secure Our World
- CISA Use Strong Passwords
- FTC: How to Avoid a Scam
- FTC: How to Recognize and Avoid Phishing Scams
- NIST Digital Identity Guidelines
Also explore related product reviews and buying guides on SenseCentral.