Top 10 Reasons Reused Passwords Create Bigger Risks
Focus keyword: reasons reused passwords create bigger risks
Learn top 10 reasons reused passwords create bigger risks with practical privacy, account security, phishing protection, device safety, Wi-Fi, and cyber hygiene advice.
Digital life now connects banking, shopping, work, family communication, photos, learning, and identity. That means privacy and security are not only technical topics; they are everyday habits. The strongest protection usually comes from simple routines repeated consistently: unique passwords, multi-factor authentication, software updates, safer browsing, careful sharing, and faster responses when something feels unusual.
This guide on Top 10 Reasons Reused Passwords Create Bigger Risks is written for everyday users, families, remote workers, creators, and small business owners who want practical protection without fear or confusion. You will find a quick comparison table, ten detailed sections, a checklist, FAQs, internal SenseCentral links, trusted external references, and useful creator resources.
Good digital safety is not about panic. It is about reducing easy risks before they become expensive, stressful, or difficult to reverse.
Table of Contents
- Quick Comparison Table
- 1. Use unique passwords for every account
- 2. Store passwords in a reputable password manager
- 3. Turn on multi-factor authentication
- 4. Replace weak security questions
- 5. Review recovery email and phone details
- 6. Remove old logged-in devices
- 7. Change passwords after breach alerts
- 8. Avoid sharing accounts casually
- 9. Protect email accounts first
- 10. Keep backup codes in a safe place
- Practical Checklist
- FAQs
Quick Comparison Table
The table below gives a fast overview of the main ideas in this post. Use it as a quick reference, then continue into the detailed explanations.
| Reason | Impact | What to do next |
|---|---|---|
| Use unique passwords for every account | Reduces account exposure, privacy leakage, scam pressure, or recovery difficulty. | Start with your most important accounts and devices first. |
| Store passwords in a reputable password manager | Reduces account exposure, privacy leakage, scam pressure, or recovery difficulty. | Start with your most important accounts and devices first. |
| Turn on multi-factor authentication | Reduces account exposure, privacy leakage, scam pressure, or recovery difficulty. | Start with your most important accounts and devices first. |
| Replace weak security questions | Reduces account exposure, privacy leakage, scam pressure, or recovery difficulty. | Start with your most important accounts and devices first. |
| Review recovery email and phone details | Reduces account exposure, privacy leakage, scam pressure, or recovery difficulty. | Start with your most important accounts and devices first. |
1. Use unique passwords for every account
Use unique passwords for every account matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
2. Store passwords in a reputable password manager
Store passwords in a reputable password manager matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
3. Turn on multi-factor authentication
Turn on multi-factor authentication matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
4. Replace weak security questions
Replace weak security questions matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
5. Review recovery email and phone details
Review recovery email and phone details matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
6. Remove old logged-in devices
Remove old logged-in devices matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
7. Change passwords after breach alerts
Change passwords after breach alerts matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
8. Avoid sharing accounts casually
Avoid sharing accounts casually matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
9. Protect email accounts first
Protect email accounts first matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
10. Keep backup codes in a safe place
Keep backup codes in a safe place matters because many privacy and security problems begin as small, ordinary actions. A person clicks quickly, shares too much, ignores an update, or keeps using an old account because it feels convenient. Over time, those choices create openings for scams, data exposure, tracking, and account takeover. The safer habit is to treat your digital life as a connected system instead of isolated apps.
To apply this habit, begin with the account, device, or setting that protects the most sensitive information. Use a written checklist, repeat the review monthly, and make the process simple enough for family members to follow. The goal is not perfect security. The goal is to remove the easy weaknesses that attackers, scammers, and data-hungry services commonly exploit.
Practical Checklist for Everyday Use
Start with your email account because it often controls password resets for many other services. Use a unique password, turn on multi-factor authentication, review recovery options, and check active sessions. Next, protect banking, shopping, cloud storage, social media, and work accounts. Update your phone, computer, browser, router, and important apps. Remove unused apps, revoke unnecessary permissions, and back up important files.
For families, keep the conversation friendly. People report mistakes faster when they do not fear blame. For remote workers, separate work data from personal browsing and report suspicious messages quickly. For everyday users, the most valuable routine is to pause before reacting to urgent messages, payment requests, or account warnings.
Key Takeaways
- Small privacy and security habits become powerful when repeated consistently.
- Unique passwords, MFA, updates, backups, and phishing awareness protect more than most people realize.
- Privacy settings should be reviewed before there is a problem, not only after one.
- Families, remote workers, and creators benefit from simple shared rules and response checklists.
Explore Our Powerful Digital Products
Browse these high-value bundles for website creators, developers, designers, startups, content creators, and digital product sellers. If you want ready-made templates, planners, UI kits, spreadsheets, startup resources, or creative assets, this store can save hours of manual work.
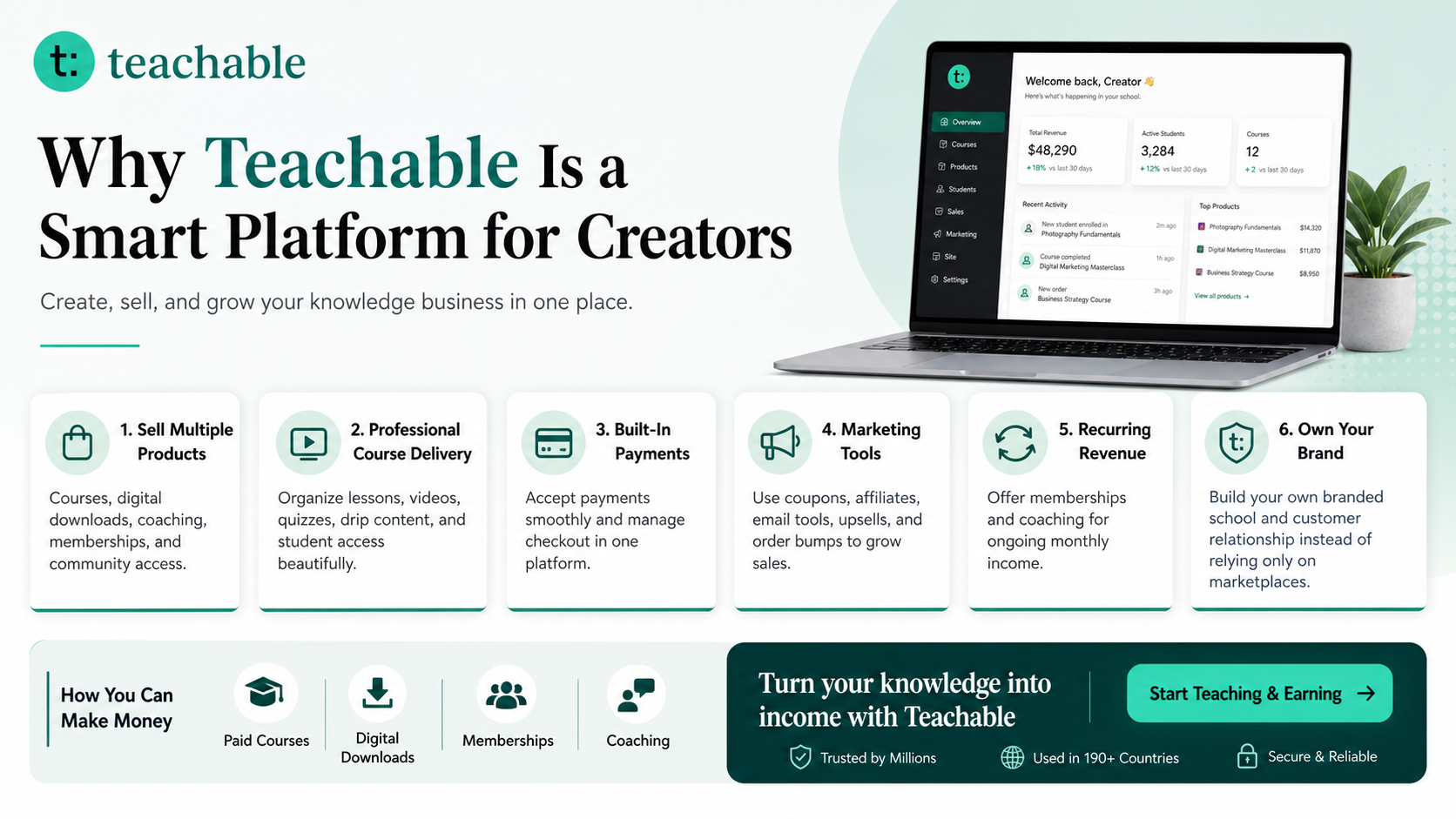
Useful Creator Resource: Try Teachable
Teachable is an online platform that lets creators build, market, and sell courses, digital downloads, coaching, and memberships. It helps educators and entrepreneurs turn their knowledge into a branded digital business without needing complex coding.
Learn more on SenseCentral: How to Make Money with Teachable: A Complete Creator’s Guide
Further Reading on SenseCentral
Useful External Resources
References
- CISA Secure Our World: https://www.cisa.gov/secure-our-world
- CISA Recognize and Report Phishing: https://www.cisa.gov/secure-our-world/recognize-and-report-phishing
- FTC Online Security: https://consumer.ftc.gov/online-security
- FTC Phishing Scams Guide: https://consumer.ftc.gov/articles/how-recognize-avoid-phishing-scams
- NIST Small Business Information Security: https://csrc.nist.gov/pubs/ir/7621/r1/final
- Google Safe Browsing: https://safebrowsing.google.com/
Featured Image Direction
A premium horizontal 16:9 digital illustration for ‘Top 10 Reasons Reused Passwords Create Bigger Risks’, deep navy and electric blue gradient background, glowing shield, lock icons, secure devices, subtle network lines, clean modern tech style, professional blog cover, no tiny unreadable text, no watermark.
FAQs
Do I need advanced technical knowledge to follow these tips?
No. The strongest everyday protection often comes from simple repeated actions: unique passwords, multi-factor authentication, software updates, careful link checking, privacy setting reviews, and reliable backups.
Which account should I protect first?
Protect your main email account first because it often controls password resets for many other accounts. Then protect banking, payment, shopping, cloud storage, and social accounts.
How often should I review privacy and security settings?
A monthly mini-review is enough for most people. Do a faster review after suspicious alerts, travel, device loss, major app changes, or any message that suggests your account may have been accessed.
Are paid security tools necessary for everyone?
Not always. Built-in protections, password managers, MFA, updates, backups, and safer browsing handle many common risks. Paid tools may help families, remote workers, and businesses that need extra monitoring or centralized controls.