Build a password reset flow securely

Build a password reset flow securely is one of those practical skills that can make a developer’s work cleaner, faster, and easier to maintain. For a site like SenseCentral, where readers compare tools, digital products, software platforms, and business workflows, this topic is especially useful because it connects technical execution with real-world results. A beautiful interface is not enough if the project structure is messy. A powerful API is not enough if it is insecure, undocumented, or difficult to scale. This guide explains the concept in a practical way so beginners, freelancers, startup founders, and working developers can apply it immediately.
The goal is not to memorize one perfect pattern. The goal is to understand the decisions behind the pattern. Good backend APIs, SaaS platforms, admin panels, marketplaces, and automation systems should be simple when the product is small, flexible when the product grows, and disciplined enough that future features do not become painful. Throughout this post, you will find a table of contents, comparison tables, implementation steps, mistakes to avoid, FAQs, useful resources, and references you can revisit while building your next product.
Post Keywords: web development, developer tools, software engineering, SenseCentral guide, digital products, SaaS, best practices, UI UX
Why This Topic Matters
Modern web projects are judged by speed, clarity, trust, and maintainability. Users rarely care which library, package, or architecture you used; they care whether the page loads quickly, the interface is understandable, the form works, the data is safe, and the product solves their problem. Developers, however, must care about the underlying structure because structure decides how quickly the product can improve.
Build a password reset flow securely matters because it sits at the point where technical decisions become user experience. A folder structure affects onboarding. State management affects bugs. API design affects frontend productivity. Authentication affects trust. Design tokens affect brand consistency. Observability affects how quickly teams fix production issues. These topics may look separate, but together they create the foundation for professional web products.
For creators and entrepreneurs, this is even more important. A digital product store, course platform, review website, or SaaS dashboard may begin as a small project, but if the structure is weak, each new feature becomes harder. The best time to create good habits is before the project becomes complicated.
Core Concepts
A secure password reset flow should not reveal whether an email address exists. The API can always return a generic success message, then send a time-limited, single-use reset link if the account exists. Reset tokens should be random, hashed in the database, expire quickly, and become invalid after use.
After a successful reset, consider invalidating active sessions or refresh tokens. Also rate limit reset requests to reduce abuse.
The core idea is to create a system that is easy to reason about. A system does not have to be large. It can be a naming convention, a folder pattern, a reusable component, a response format, a validation schema, or a simple checklist. What matters is that the pattern reduces repeated decisions and helps people build consistently.
When evaluating any technical approach, ask four questions: Does it make the user experience clearer? Does it make future development easier? Does it reduce risk? Does it match the current size of the project? If the answer is yes, the pattern is probably useful. If the answer is no, it may be decoration disguised as architecture.
Comparison Table
The table below summarizes common approaches and when they make sense. Use it as a decision guide, not as a rigid rule.
| Approach | Best For | Main Benefit | Watch Out For |
|---|---|---|---|
| Simple controller-service pattern | Small APIs and MVPs | Clear separation without too much complexity | Can grow messy without standards |
| Layered architecture | Production SaaS and marketplaces | Better testing, security, and maintainability | More files and decisions upfront |
| Event-driven flow | Webhooks, billing, notifications, jobs | Reliable background processing | Needs queues, retries, and observability |
| Microservice approach | Large teams and independent domains | Independent scaling and ownership | Operational overhead and distributed debugging |
Step-by-Step Implementation
- Start with a threat model: what must be protected and who can access it?
- Use secure password hashing, short-lived tokens, and carefully scoped sessions.
- Store secrets outside source code and rotate them when needed.
- Rate limit sensitive endpoints such as login, password reset, and magic link requests.
- Log security events without storing raw passwords or sensitive tokens.
After implementing the first version, create a small review checklist. Does it work on mobile? Does it handle loading and errors? Is the naming clear? Can another developer understand it? Is sensitive data protected? Does the page or API provide useful feedback? These practical questions reveal weaknesses before users experience them.
Example Pattern
The exact code will vary by stack, but a small example helps translate the idea into implementation. Treat the snippet below as a starting point and adapt it to your own project structure, validation rules, and design conventions.
{
"success": false,
"error": {
"code": "VALIDATION_ERROR",
"message": "Please check the highlighted fields."
}
}The important part is not copying the snippet line by line. The important part is understanding the pattern: name things clearly, keep responsibilities separate, handle edge cases, and make the next change easier.
Best Practices Checklist
- Keep the first version understandable enough that another developer can maintain it.
- Create repeatable patterns for naming, file placement, error handling, loading states, and documentation.
- Make user trust a design requirement: clear messages, secure flows, accessible controls, and predictable behavior.
- Document decisions in short notes so future changes do not break the original intent.
- Review the implementation after real use; production behavior often teaches what planning cannot.
How to Apply This in a Real Business Website
For product review websites, affiliate websites, SaaS landing pages, learning platforms, and digital product stores, the technical pattern should support the business goal. That means faster publishing, clearer user journeys, stronger trust signals, better conversion tracking, and fewer maintenance problems. A frontend feature should guide visitors toward the right decision. A backend feature should protect data, automate work, and make the product reliable. When technology supports the business model, development becomes an asset instead of an expense.
If you are building a review article, comparison page, template store, course platform, or small SaaS product, document your reusable sections and backend flows. Over time you can turn them into internal tools, starter kits, templates, or even digital products. This is how a single development skill can become a repeatable business advantage.
Common Mistakes to Avoid
- Starting with complexity: Beginners often copy enterprise architecture before the product needs it. Start with a clean baseline, then evolve.
- Skipping naming conventions: A project without naming rules becomes harder to search, document, and onboard.
- Ignoring edge cases: Empty states, loading states, validation failures, permission failures, slow networks, and retries are part of real software.
- Forgetting security and accessibility: Beautiful interfaces and fast APIs still fail when users cannot trust or use them safely.
- No measurement: Performance, errors, conversion, and usage patterns should be measured so improvements are based on evidence.
Useful Resources for Builders, Creators, and Digital Product Sellers
Explore Our Powerful Digital Products: Browse high-value bundles for website creators, developers, designers, startups, content creators, and digital product sellers. These resources can help you build faster, design better, package your knowledge, and create more polished digital offers.
Explore Our Powerful Digital Products
Turn Your Knowledge Into a Sellable Digital Business
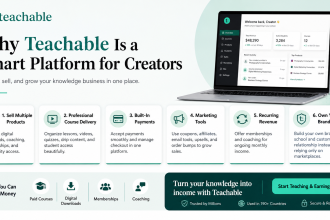
Teachable is an online platform that lets creators build, market, and sell courses, digital downloads, coaching, and memberships. It helps educators and entrepreneurs turn their knowledge into a branded digital business without needing complex coding.
Learn more: How to Make Money with Teachable: A Complete Creator’s Guide
Further Reading on SenseCentral
- SenseCentral Home — explore more guides, comparisons, and product reviews.
- Web Development Guides — tutorials for frontend, backend, automation, and online business tools.
- Digital Products & Creator Business — resources for selling downloads, templates, courses, and bundles.
- How to Make Money with Teachable: A Complete Creator’s Guide — a useful guide for turning expertise into digital products.
FAQs
Is Build a password reset flow securely suitable for a small MVP?
Yes, but keep the first version simple. Use the principle behind the pattern rather than over-engineering a large architecture before users arrive.
What is the biggest backend mistake beginners make?
They often trust input too early, mix business logic into route handlers, skip logs, and add authentication without thinking through refresh, revoke, and recovery flows.
Should I use Node.js and Express for production APIs?
Node.js and Express can work well in production when you add validation, security headers, rate limits, structured errors, monitoring, and a disciplined deployment process.
How much documentation does an API need?
Enough for another developer to understand endpoints, authentication, request examples, response formats, errors, limits, and versioning rules without asking the original developer.
When should I move beyond a monolith?
Move beyond a monolith when team boundaries, scaling needs, release cycles, or domain complexity justify the operational cost. Many profitable products can stay monolithic for a long time.
Key Takeaways
- Build a password reset flow securely is most valuable when it improves both developer workflow and user experience.
- Start simple, but use patterns that can grow without forcing a full rewrite.
- Document the decisions behind your structure, not just the final code.
- Security, accessibility, performance, and maintainability should be included from the beginning.
- Useful resources, templates, and platforms can speed up execution when used with clear strategy.